Who Is Really Responsible For Cloud Security?
The added agility and cost-effectiveness rendered to the business organizations make cloud solutions a viable investment. However, narrowing down to a reliable cloud storage platform along with remaining proactive about personalized security measures becomes pivotal. Regardless of enterprise needs or individual cloud requirements, there remains a much-needed discussion regarding cloud security so that sensitive files and personal information can be in safe hands. If you’re going ahead with a trusted cloud storage platform like houm.me, be conscientious about who is accountable for preserving your data when most companies trail around a shared responsibility model.
This article aims to examine the security of cloud storage solutions and whose shoulders does the security of your data land on. With first-time users, a prevalent misconception lies in the belief of relying almost entirely on their cloud service when it comes to data security. However, the shared responsibility model tends to address the elephant in the room, chalking down your part in the process of keeping your cloud data secure. Read on to assess what this model entails and how you can maximize the security of numerous files uploaded on your cloud server.
What does the shared responsibility model mean?
This model primarily outlines the structure of accountability of data security in any cloud infrastructure such that the vendor, as well as the enterprise (or individual), holds the responsibility. Put in simpler words; shared responsibility model states that your cloud service provider (CSP) will be answerable for the security “of” their cloud infrastructure. This way, CSPs have to remain mindful of keeping their storage facilities, computing systems, as well as network service layers robust and secure. Having an inherently strong infrastructure calls for numerous measures that need to be in place so as to lay down an impermeable ground for the stored data.
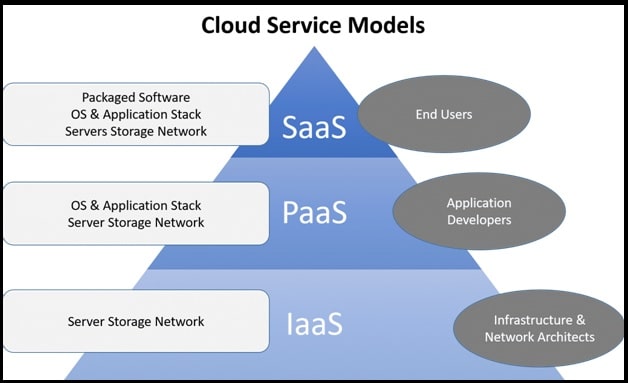
The enterprise uploading terabytes of files, on the other hand, remains accountable for the security “in” the cloud network. This part of the shared responsibility model makes clear that an enterprise has to have a secure cloud environment in which software, data, and underlying services function privately and safely. Typically, private, public, and SaaS —these are three primary service models that further impact the way responsibility of data security persists in a cloud network.
Breaking down cloud service models
As aforementioned, these different service models have a varied structure of security division, which is why you need to handpick the one that seems most promising and feasible. As businesses move towards adopting a public or SaaS model, cloud security becomes more inclined towards the service provider. Nonetheless, keeping the data flowing in the system secure, is something that always remains an inescapable duty of an enterprise despite the service model put into effect.
- Private
In a private cloud infrastructure, the enterprise is solely accountable for all the operations pertaining to the security of present data. As the cloud system in private cloud solutions is hosted locally, enterprises have to secure their data centers on their own. Private models are specifically chosen when it’s feasible to manage service configurations, infrastructure needs, OS security, physical and virtual networks, hypervisor, firewall management, etc. With this service model, ownership remains in the hands of the enterprise —therefore, ensuring its utmost security with the help of identity and access management becomes quintessential.
- Public
With a public cloud in place, the CSP assumes the responsibility of safeguarding the infrastructure they own. This includes instilling security measures to readily keep up with the safety of their physical networks, as well as the hypervisor. On the flip side, ensuring data security still falls in the hands of the enterprise carrying out operations within that public cloud. This means managing virtual networks, workload, identity and access, applications, etc., falls into the bucket of the enterprise.
- SaaS
Apart from ensuring physical security and that of the infrastructure, SaaS cloud providers also take up the responsibility of keeping the applications secure. However, this doesn’t include being accountable for the way these applications are used within your enterprise or by your customers. If you’re taking up a SaaS cloud model, exercising means for preventing data breaches and other infiltrations becomes pivotal.
Need for physical security in a cloud network
With the shift towards digital data management, enterprises often find it elective to consider physical security measures. Therefore, it becomes rudimentary to understand that not everything in a cloud network can be left upon your service provider. As your device management, servers, office location, power regulation, employees, etc. determine the overall security of your infrastructure, these factors have a crucial impact on cloud security.
Best practices for the shared responsibility model
? Focus on managing the risks in your internal system so that vulnerabilities can be identified beforehand.
? If you’re shifting from a traditional IT infrastructure to a cloud-based one, be watchful of measures that can maintain a balance so as to facilitate the change.
? Be precise with your security needs so that looking for a suitable cloud solutions doesn’t have to be too arbitrary.
? When selecting a public or SaaS model, get into an in-depth discussion with your cloud service provider regarding the extent of responsibility that they’re going to cover. Along with this, ascertain what all you have to be accountable for in terms of securing your cloud network.
? Document every responsibility measure so that you can have a solid ground to turn to whenever there’s a conflict that demands immediate attention.
Takeaway: cloud security demands a team effort
All in all, cloud services need to be chosen with a definite responsibility matrix so that you can actively decide your responsibility as well as that of your vendor’s. As your IT infrastructure also plays a critical role in keeping the cloud network secure, ensure you’ve kept it updated with the latest technological tools. How secure your cloud network turns out to be can only be decided when you, as well as the CSP is carrying out measures to keep the data safe under the shared responsibility model.
| Author Bio:
Samiksha Jain is an expert in information security management and a writer by profession at Walnut Folks. In technical writing for 6 years, she makes complex topics interesting to the general audience. She loves going on long drives in her spare time. |